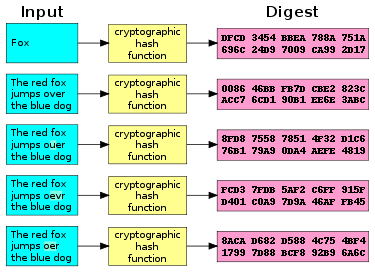
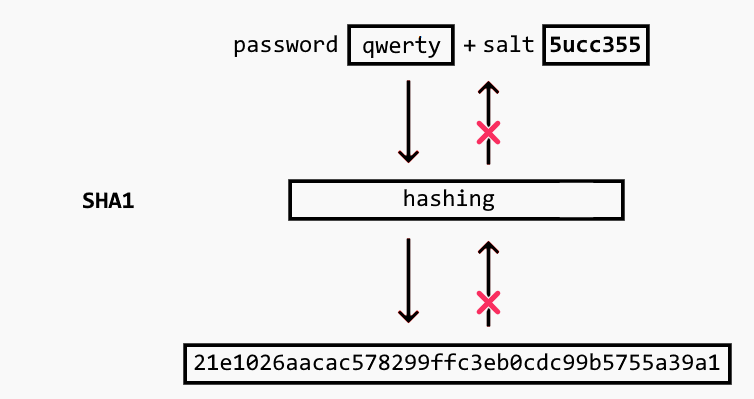
SHA-1 Cryptographic hash function Secure Hash Algorithms SHA-2, salt, angle, text, symmetry png | PNGWing
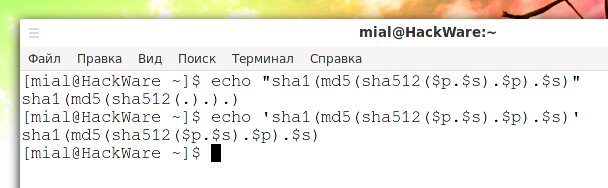
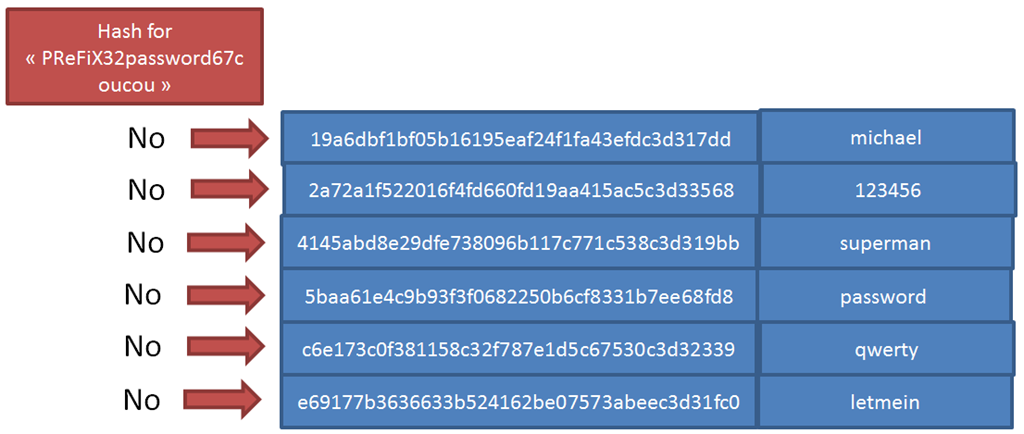
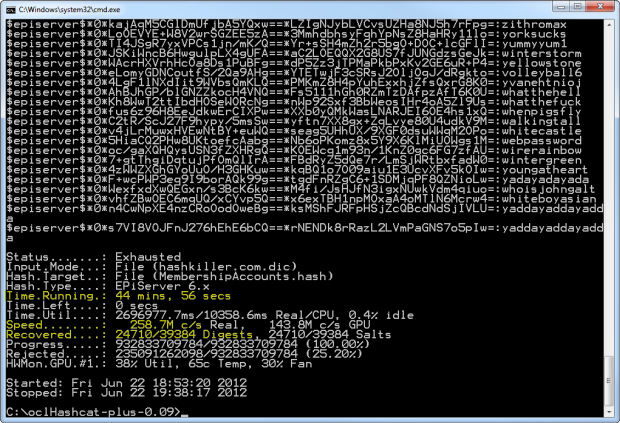
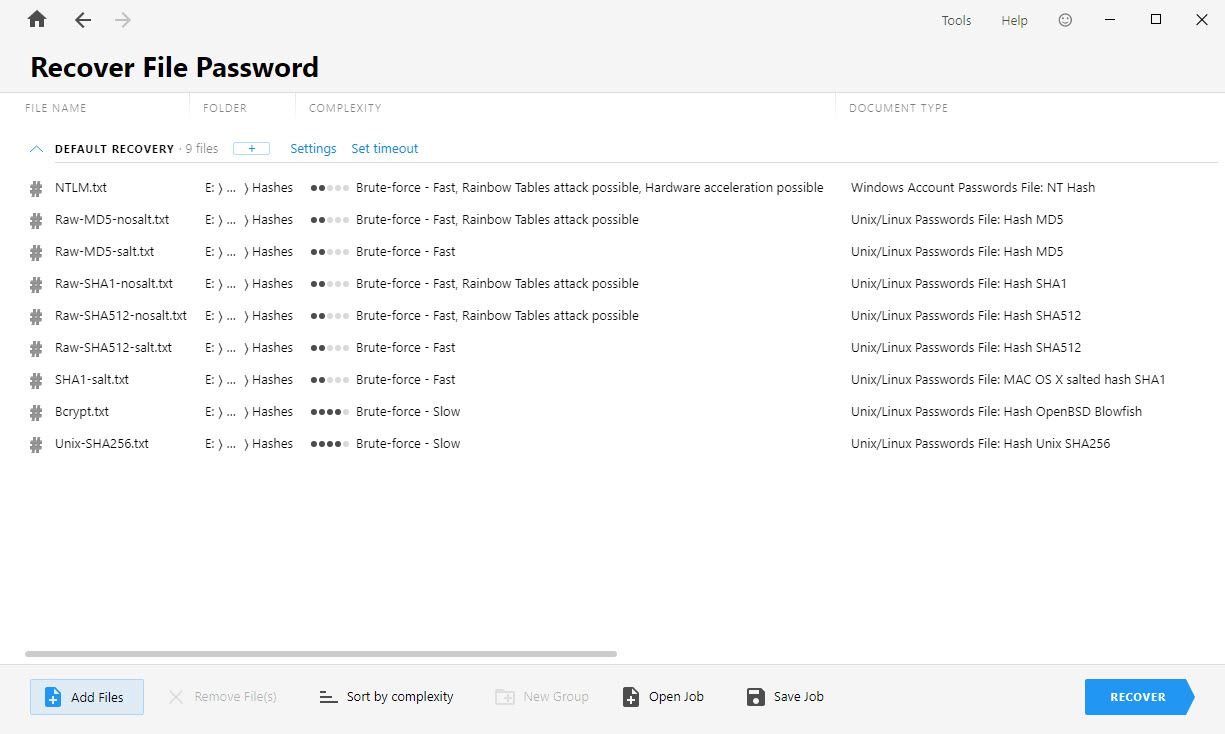
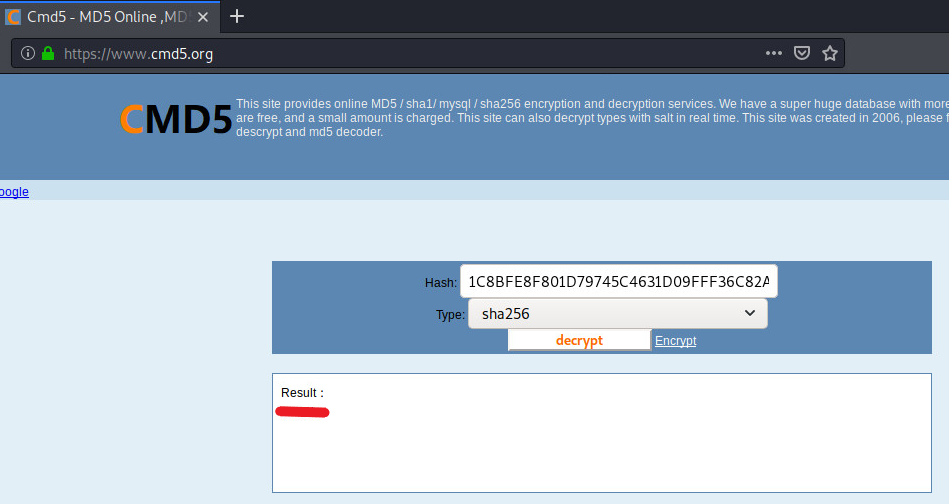
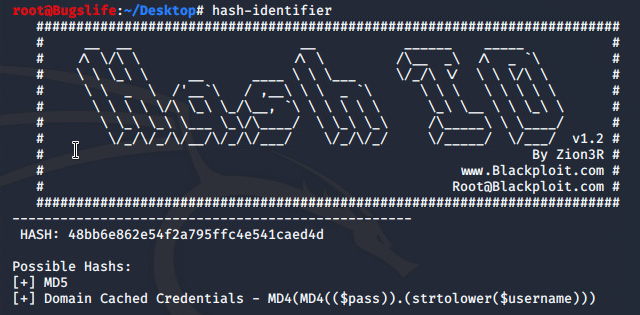
Comprehensive Guide to John the Ripper. Part 6: How to brute force non-standard hashes - Ethical hacking and penetration testing

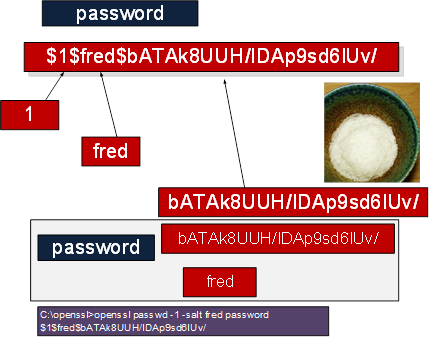
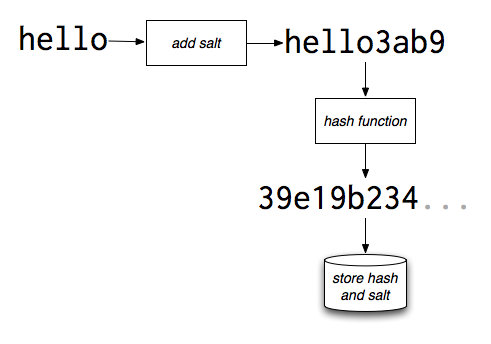
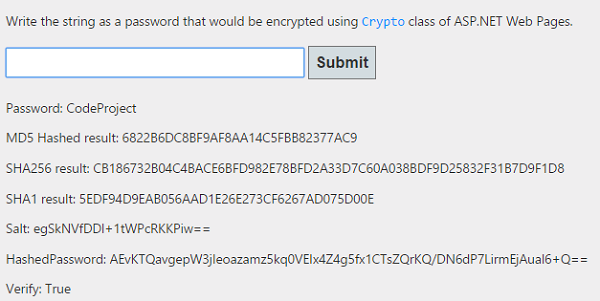
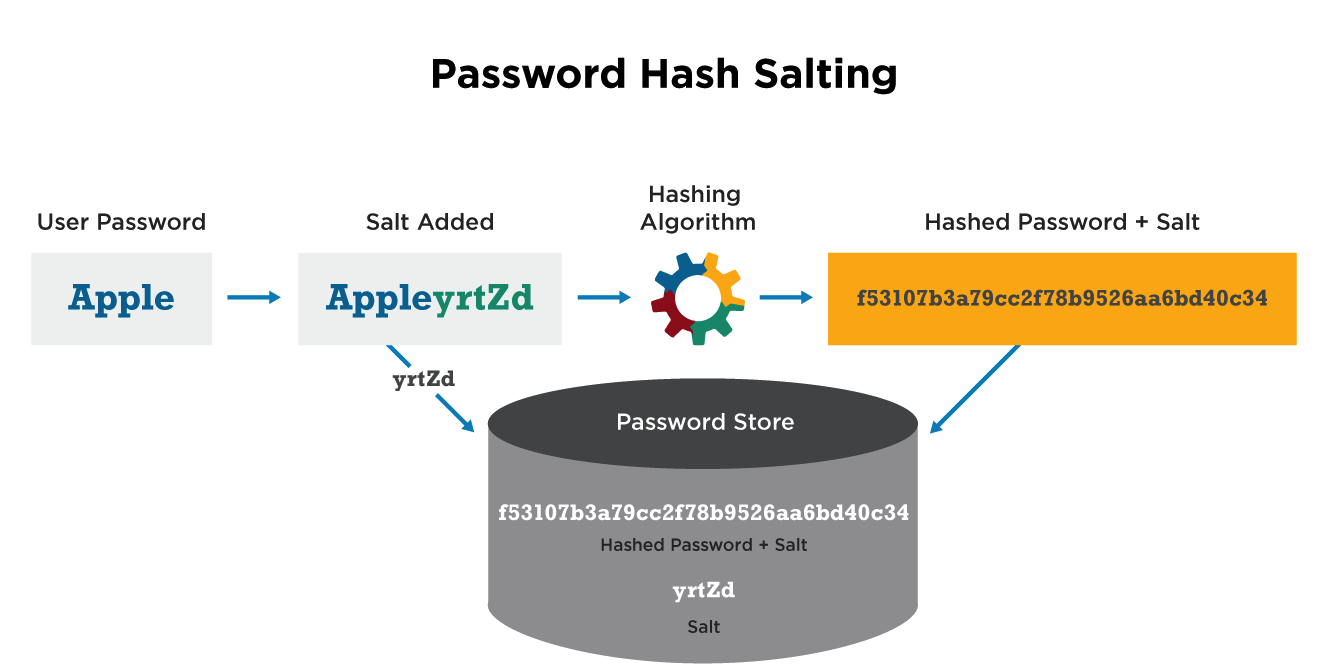
Salted Hash Generator : Free All-in-one Tool to Generate Salted Hash for MD5/SHA1/SHA256/SHA512/LM/NTLM | www.SecurityXploded.com